ArgoCD Setup on Kubernetes/OpenShift Cluster
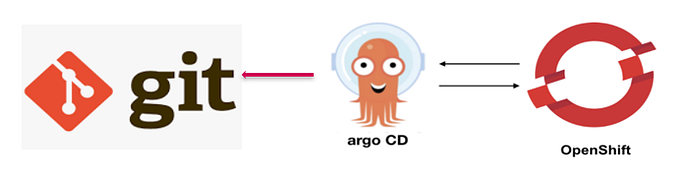
ArgoCD is a declarative GitOps tool built to deploy applications to Kubernetes/OpenShift clusters.
ArgoCD is a Kubernetes/OpenShift controller, responsible for continuously monitoring all running applications and comparing their live state to the desired state specified in the Git repository.
Setup ArgoCD on OpenShift Cluster
Follow below steps to setup ArgoCD onto your OpenShift cluster.
Step 1: Create Project namespace
To set up a Argo CD instance, create an argocd instance namespace on OpenShift as its uses dedicated namespaces to run the instance.
ArgoCD will need to run on its on Namespace. Let’s create it:
--- Create dedicated Namespace---
$ oc create namespace argocdStep 2: Apply the ArgoCD Manifest on OpenShift
Now we can perform the actual installation of ArgoCD on OpenShift cluster by running the installation manifest.
$mkdir argocd
$cd argocd
$wget https://raw.githubusercontent.com/argoproj/argo-$cd/stable/manifests/install.yaml
$oc apply -n argocd -f ./install.yamlOutput:
customresourcedefinition.apiextensions.k8s.io/applications.argoproj.io created
customresourcedefinition.apiextensions.k8s.io/appprojects.argoproj.io created
serviceaccount/argocd-application-controller created
serviceaccount/argocd-dex-server created
serviceaccount/argocd-server created
role.rbac.authorization.k8s.io/argocd-application-controller created
role.rbac.authorization.k8s.io/argocd-dex-server created
role.rbac.authorization.k8s.io/argocd-server created
clusterrole.rbac.authorization.k8s.io/argocd-application-controller created
clusterrole.rbac.authorization.k8s.io/argocd-server created
rolebinding.rbac.authorization.k8s.io/argocd-application-controller created
rolebinding.rbac.authorization.k8s.io/argocd-dex-server created
rolebinding.rbac.authorization.k8s.io/argocd-server created
clusterrolebinding.rbac.authorization.k8s.io/argocd-application-controller created
clusterrolebinding.rbac.authorization.k8s.io/argocd-server created
configmap/argocd-cm created
configmap/argocd-rbac-cm created
configmap/argocd-ssh-known-hosts-cm created
configmap/argocd-tls-certs-cm created
secret/argocd-secret created
service/argocd-dex-server created
service/argocd-metrics created
service/argocd-redis created
service/argocd-repo-server created
service/argocd-server-metrics created
service/argocd-server created
deployment.apps/argocd-application-controller created
deployment.apps/argocd-dex-server created
deployment.apps/argocd-redis created
deployment.apps/argocd-repo-server created
deployment.apps/argocd-server createdThe pods will be started in a few seconds or minutes.

Check if the updated Dex pod is running by executing the following command:

Step 3: Get the ArgoCD Server password
Once you confirm all pods are running, get the ArgoCD Server initial pwd which is autogenerated.
$ARGOCD_SERVER_PASSWORD=$(oc -n argocd get pod -l "app.kubernetes.io/name=a
Confirm the password was saved.

Step 4: Expose ArgoCD Server using OpenShift Route
We need to Patch ArgoCD Server deployment on OpenShift for the service to be exposed through the OpenShift Route:
$oc -n argocd patch deployment argocd-server -p '{"spec":{"template":{"spec":{"$setElementOrder/containers":[{"name":"argocd-server"}],"containers":[{"command":["argocd-server","--insecure","--staticassets","/shared/app"],"name":"argocd-server"}]}}}}'You should get patched in the output if above command was successful.
$deployment.apps/argocd-server patchedNow you can proceed to expose ArgoCD Server:
$oc -n argocd create route edge argocd-server --service=argocd-server --port=http --insecure-policy=RedirectConfirm the route is created.
$ oc get route -n argocd NAME HOST/PORT PATH SERVICES PORT TERMINATION WILDCARD argocd-server argocd-server-argocd.apps.mycluster.example.com argocd-server http edge/Redirect None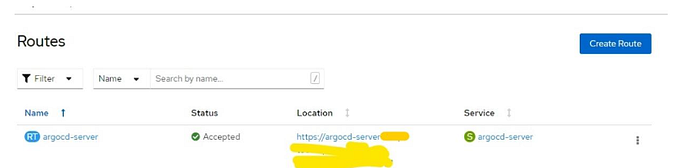
Check if the web console is accessible by navigating to the location provided by executing the following command:
$echo https://$(oc get routes argocd-server -o=jsonpath='{ .spec.host }')You can update the host name used in the route by editing the yaml configuration on the fly:
$ oc edit route -n argocdStep 5: Download Argo CD CLI
Download the lasted available version of argoCD client from release page
$ VERSION=$(curl --silent "https://api.github.com/repos/argoproj/argo-cd/releases/latest" | grep '"tag_name"' | sed -E 's/.*"([^"]+)".*/\1/')
curl -sSL -o /usr/local/bin/argocd https://github.com/argoproj/argo-cd/releases/download/$VERSION/argocd-linux-amd64Now lets make the argocd CLI executable:
$sudo chmod +x /usr/local/bin/argocdLets check argocd client version:
$ argocd version --client
argocd: v1.5.5+0fdef48
BuildDate: 2020-05-16T04:02:57Z
GitCommit: 0fdef4861e12026e133224f7c9413072340e2983
GitTreeState: clean
GoVersion: go1.14.1
Compiler: gc
Platform: linux/amd64Using the username admin and the password to login to Argo CD’s IP or hostname:
--- Get routes ---
ARGOCD_ROUTE=$(oc -n argocd get route argocd-server -o jsonpath='{.spec.host}')--- Get Admin password ---
ARGOCD_SERVER_PASSWORD=$(oc -n argocd get pod -l "app.kubernetes.io/name=argocd-server" -o jsonpath='{.items[*].metadata.name}')--- Login to ArgoCD API ---
argocd --insecure --grpc-web login ${ARGOCD_ROUTE}:443 --username admin --p
Change the password using the command:
argocd --insecure --grpc-web --server ${ARGOCD_ROUTE}:443 account update-pasStep 6: Access ArgoCD Dashboard
You can then access the ArgoCD console with the route URL.

The login credentials will be
Username: admin
The initial Password can be obtained with:
$kubectl get pods -n argocd -l app.kubernetes.io/name=argocd-server -o name | cut -d'/' -f 2Once you’ve logged in, you should see the below page.
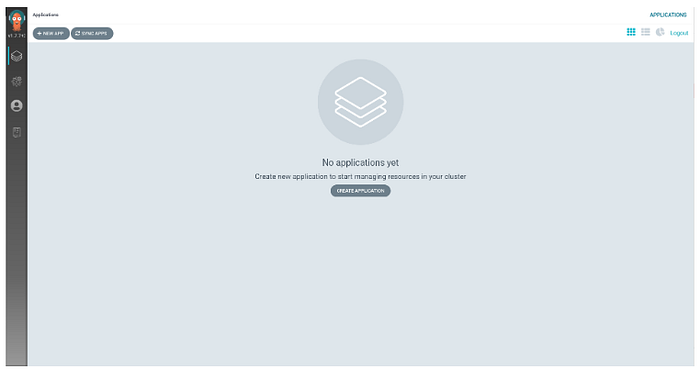
This is the Argo CD Web UI.
Resetting admin Password
By default the password is set to the name of the server pod.
To change the password, you need to:
- Edit the
argocd-secretsecret - Update the
admin.passwordfield with a new bcrypt hash.
Note: This blog is based on my own-experiences and learning from different sources available on the cloud.
………………………………….Thanks for reading……………………………
